Targets of Russian Cyber Operations Face Account Takeovers
Recent reports confirm that encrypted messaging service Signal has been subjected to a series of sophisticated social engineering attacks. These incidents, primarily targeting high-profile individuals including journalists and government officials, have resulted in account takeovers, but crucially, have not compromised Signal's underlying end-to-end encryption or its infrastructure. The attackers have employed tactics that rely on victim compliance rather than exploiting technical vulnerabilities within the app itself.

Scope of Attacks: Reports indicate around 300 Signal accounts belonging to politically connected individuals in Germany were targeted.
Attribution: These campaigns have been linked to Russia-based hackers, with German media noting the "brazenness" of the operations. The FBI and CISA also issued a warning in March stating Signal had become a primary target of Russian intelligence-linked hackers.
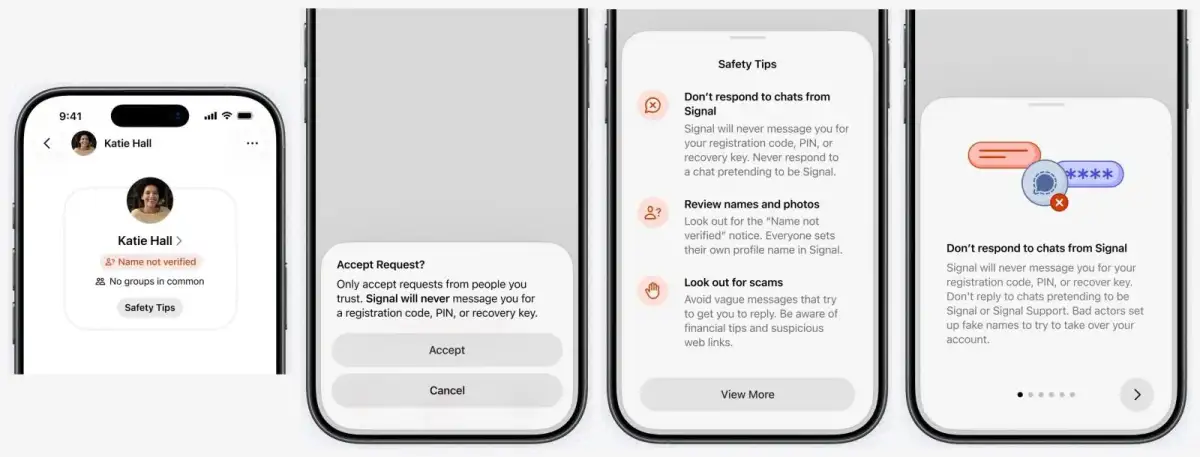
Nature of Exploitation: The attacks did not involve a data breach of Signal's encryption. Instead, attackers tricked users into divulging sensitive authentication information, such as registration codes, PINs, or recovery keys.
Protections and Warnings Issued
In response to these escalating threats, both security authorities and Signal itself have implemented new measures and issued advisories. The UK's National Cyber Security Centre (NCSC), alongside Dutch intelligence agencies, has been instrumental in flagging these campaigns and advising individuals on defensive strategies.

"High-risk individuals have been urged to take steps to reduce their exposure to social engineering attacks against encrypted messaging apps, such as Signal, WhatsApp, and Facebook Messenger." - Computer Weekly
Signal has introduced new in-app security warnings and an extra confirmation step for users accepting message requests. These updates aim to alert users to potential phishing attempts and remind them to only accept requests from trusted contacts. The app now explicitly warns users that it will never ask for registration codes, PINs, or recovery keys.
Read More: AI Overconfidence Makes People Trust Wrong Answers More

Recommended User Defenses
Treat unexpected support messages as hostile.
Always check linked devices for unauthorized access.
Enable two-step verification and a strong PIN/passcode. Signal uses a registration lock, while WhatsApp offers a two-step verification PIN.
Revoke unknown logins on linked devices for both Signal and WhatsApp.
Background on the Threat Landscape
The targeting of encrypted messaging apps like Signal and WhatsApp has been ongoing, with warnings issued as early as late 2025. Cyber threat actors are leveraging spyware and advanced social engineering to compromise personal devices of high-value individuals across the US, Europe, and the Middle East.
The Dutch intelligence agency AIVD has characterized the ongoing efforts as a "large-scale global cyber campaign" by Russian state-sponsored hackers. These actors are reportedly interested in Signal and WhatsApp specifically due to their strong reputations for security, making their compromise a significant propaganda and intelligence-gathering victory. Security researchers have noted that attackers sometimes impersonate messaging app platforms themselves as part of their phishing schemes. The methods used have been reused by hackers to compromise other encrypted applications, including Telegram.