Malicious Updates Pushed to Popular JavaScript Library
A recent supply chain attack compromised the npm account of the maintainer for Axios, a widely used JavaScript library. Attackers injected malicious code into new versions of Axios, which were then distributed through the npm package registry. The tainted packages, [email protected] and [email protected], contained a transitive dependency, [email protected], which acted as a dropper for a cross-platform remote access trojan (RAT).
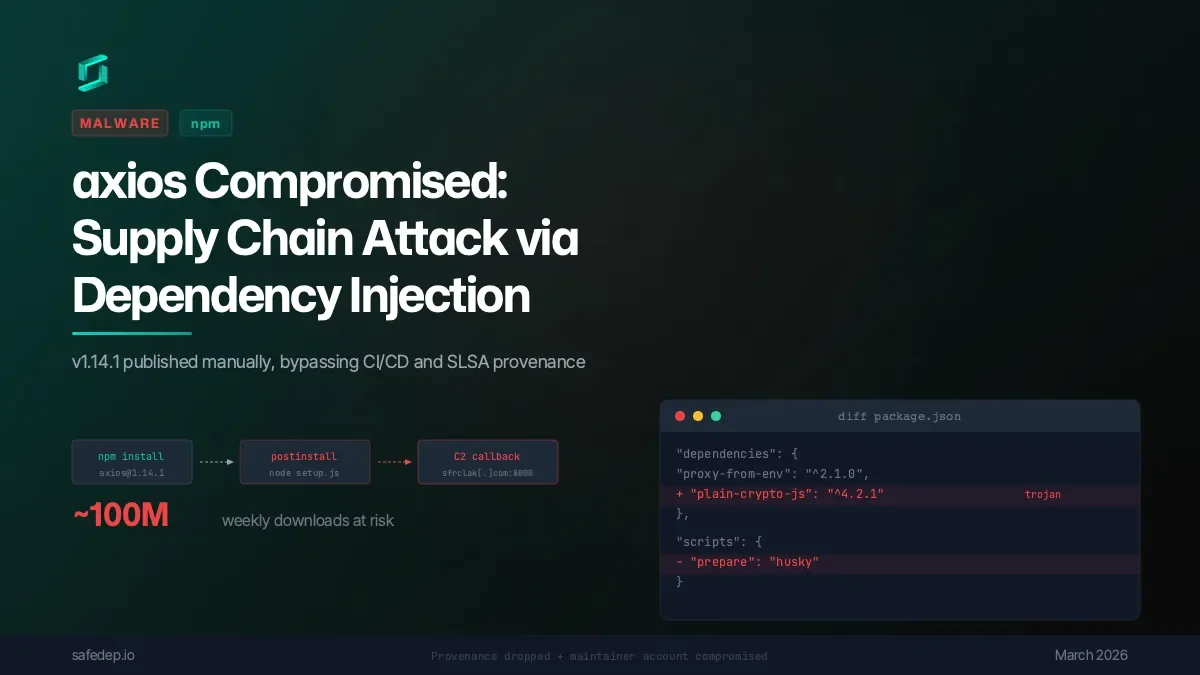
The attackers gained access to the maintainer's account, reportedly without multi-factor authentication enabled, and published the compromised versions of Axios. These malicious updates remained live on the npm registry for approximately three hours. Any developer or automated system updating Axios during this window, or pulling any package with a flexible version dependency on Axios, could have inadvertently installed the malware.
The injected malware, masquerading as a legitimate package, was designed to deliver a RAT to affected systems. The specific payload and its execution varied by operating system:
Read More: Helium shortage stops weather balloons in Canada and raises chip prices
macOS: A native binary, identified as com.apple.act.mond, was dropped into
/Library/Caches/.Windows: A PowerShell script (wt.exe) or VBScript stager was deployed.
Linux: A Python script named ld.py was used.
The command and control (C2) infrastructure for the attack was traced to sfrclak[.]com on port 8000. Security researchers noted that the malicious code was injected via a modified package.json file, without altering the core Axios source files. The attackers also published a malicious version of the plain-crypto-js package itself, serving as the primary payload carrier.
Background and Vulnerabilities
The compromise highlights critical vulnerabilities in software development workflows and package management security. The attackers exploited a time-dependent dependency resolution mechanism, meaning that systems fetching dependencies during the attack window were susceptible.
"Every npm install pulling the latest version is potentially compromised right now." - Feross Aboukhadijeh, Socket Security CEO
Key takeaways from the incident include:
Account Security: The compromise underscores the critical need for multi-factor authentication (MFA) on all developer accounts, especially those managing widely used packages.
Dependency Management: Reliance on flexible version ranges (like
^or~) inpackage.jsonfiles can lead to automatic fetching of compromised versions. Pinning dependencies to specific, safe versions ([email protected] for the 1.x branch and [email protected] for the 0.x branch) is a crucial mitigation step.Supply Chain Visibility: Security teams are increasingly looking for signals like the absence of SLSA provenance attestations, which were present in legitimate Axios versions but missing from the compromised ones.
Automated Detection: Tools capable of scanning lockfiles (
package-lock.json,yarn.lock,pnpm-lock.yaml) and installed packages for specific malicious versions or dependencies are vital for rapid identification.Mitigation Strategies: Beyond updating to safe versions, organizations are advised to consider using npm's
overridesorresolutionsin their configuration to prevent transitive resolution of the malicious dependency. Disabling script execution duringnpm install(npm config set ignore-scripts true) is also a recommended preventative measure.
Microsoft Security Intelligence has attributed the infrastructure and the Axios npm compromise to Sapphire Sleet, identified as a North Korean state actor. This incident serves as a stark reminder of the pervasive threats within the 'JavaScript supply chain', a complex web of dependencies that underpins a vast array of modern software applications.
Read More: FBI Declares Suspected China Cyberattack a Major Incident Affecting Investigations








