A profound shift in computing power, driven by advancements in quantum technology, is poised to render current digital security protocols obsolete. The impending arrival of "Q-Day," a term signifying the point at which quantum computers can crack existing encryption, presents a significant and complex challenge to global cybersecurity. Experts and technology leaders are increasingly vocal about the need for immediate preparation, warning that the window for transition to quantum-resistant solutions is narrowing.

The core issue revolves around the fundamental difference in how quantum computers process information. Unlike traditional bits, which exist as either 0 or 1, quantum computers utilize 'qubits' that can represent multiple states simultaneously, a phenomenon rooted in quantum mechanics. This inherent capability allows them to tackle complex mathematical problems with unprecedented speed, directly undermining the cryptographic algorithms that currently secure vast swathes of digital communication and data.
Read More: Relevance AI API Triggers Released 17 May 2026 for Automated Agents

The urgency is amplified by the fact that adversaries may already be collecting encrypted data, anticipating a future where it can be decrypted with quantum computing power. This "harvest now, decrypt later" strategy means that data considered secure today could be compromised retroactively. While some organizations, like HSBC and Cisco, report ongoing efforts toward quantum safety, many others, including sectors like healthcare, lag behind, indicating a disparate level of readiness.

The Race for Quantum Resilience
Major technology players, including Google, IBM, and Microsoft, are actively involved in developing scalable quantum systems and exploring new cryptographic approaches. The National Institute of Standards and Technology (NIST) is at the forefront of establishing new 'post-quantum encryption' standards, having already finalized initial quantum-resistant algorithms. These new systems rely on more intricate mathematical challenges designed to withstand quantum attacks.
Organizations are being advised to take concrete steps to prepare for this transition. These include:
Read More: Israel Kills Hamas Commander Tied to Oct 7 Attacks in Gaza
Educating senior management on the implications of Q-Day.
Identifying systems and data most vulnerable to quantum decryption.
Planning for the migration to quantum-safe encryption.
Rigorously assessing the quantum readiness of service providers.
A Shadow Over the Digital Age
The term "Q-Day" itself denotes not a fixed date, but rather a future threshold where quantum computing capabilities surpass current encryption's resilience. The timeline for this event remains a subject of debate among experts, with some suggesting it could arrive within the next two years, while others foresee a more gradual escalation.
This looming crisis is being compared to the Y2K bug, but with potentially more far-reaching and insidious consequences. Unlike Y2K, which was a more defined and visible problem, the threat of Q-Day could manifest more subtly, impacting encrypted data stored today without immediate, obvious signs. The very architecture of the internet and its security relies on the mathematical underpinnings that quantum computers threaten to dismantle.
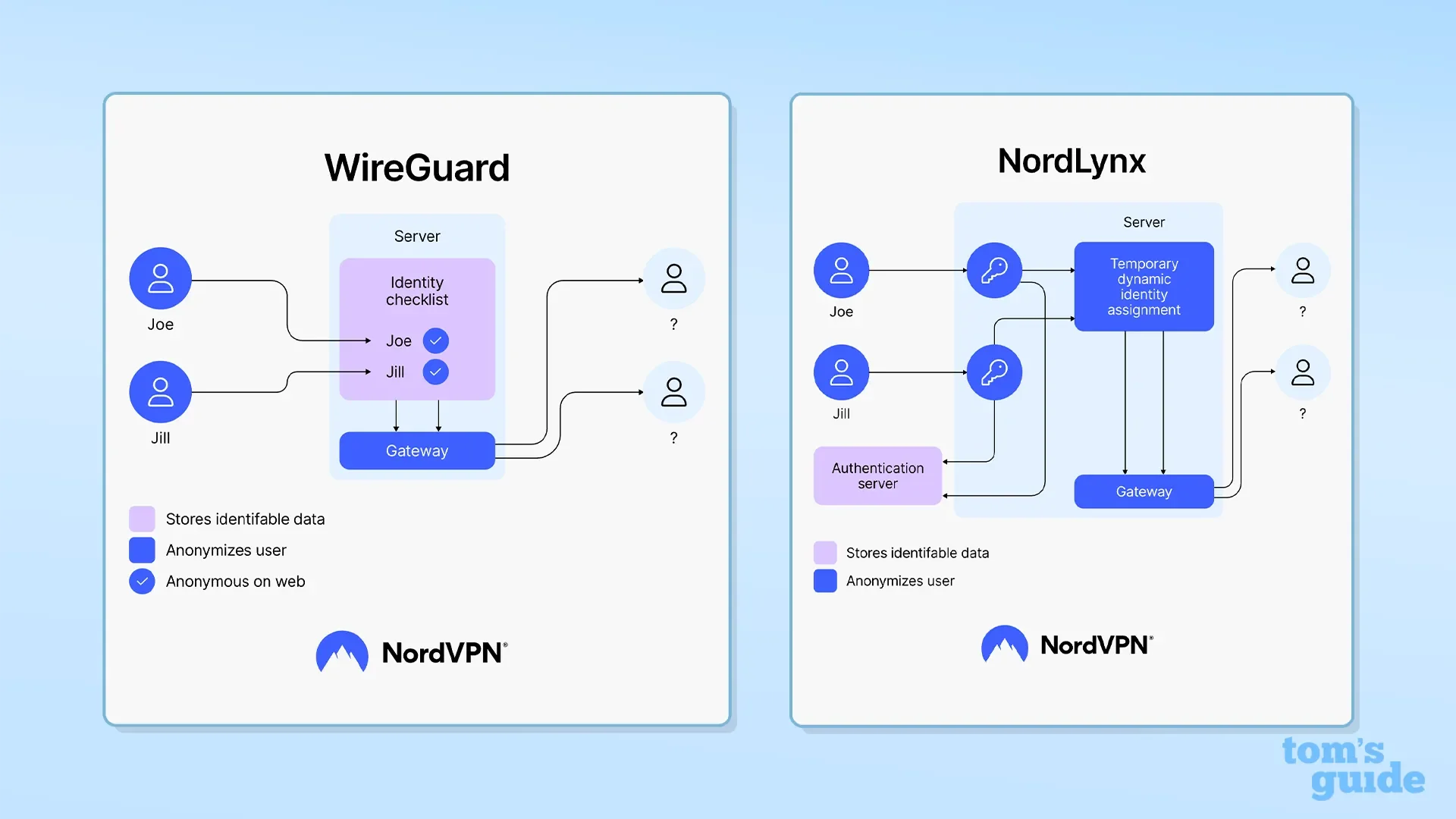
The push towards quantum readiness is not merely a technological upgrade; it represents a fundamental re-evaluation of digital security in an era where the rules of computation are being rewritten. Companies like NordVPN and ExpressVPN are already incorporating post-quantum encryption into their offerings, signaling a nascent but growing trend in the market.
Read More: TeamDynamix API Access Needs Technical Setup for Users
Background: The Quantum Frontier
Quantum computing operates on principles of quantum mechanics, employing qubits that leverage superposition and entanglement to perform calculations. This differs significantly from classical computers, which rely on binary bits. The ongoing progress in quantum hardware, despite its current power constraints, is relentless, bringing the potential for cryptographically relevant quantum computers closer to reality. This ongoing development underscores the need for proactive planning, moving beyond mere awareness to actionable strategies for a quantum-safe future.








